A cyberattack that crippled fuel supplies on the East Coast of the US and sent gas prices soaring could have been an inside job conducted by American spooks, rather than foreign hackers, a prominent Russian IT expert has claimed.
After a massive systems failure caused the Colonial Pipeline to shut down, Natalya Kaspersky, the founder and former CEO of security software firm Kaspersky Lab, as well as one of Russia’s wealthiest women, made the explosive suggestions in an interview with RIA Novosti on Friday. She alleges that the US’ top foreign intelligence agency, the CIA, has a crack team of digital warriors who are able to masquerade as overseas hacking groups.
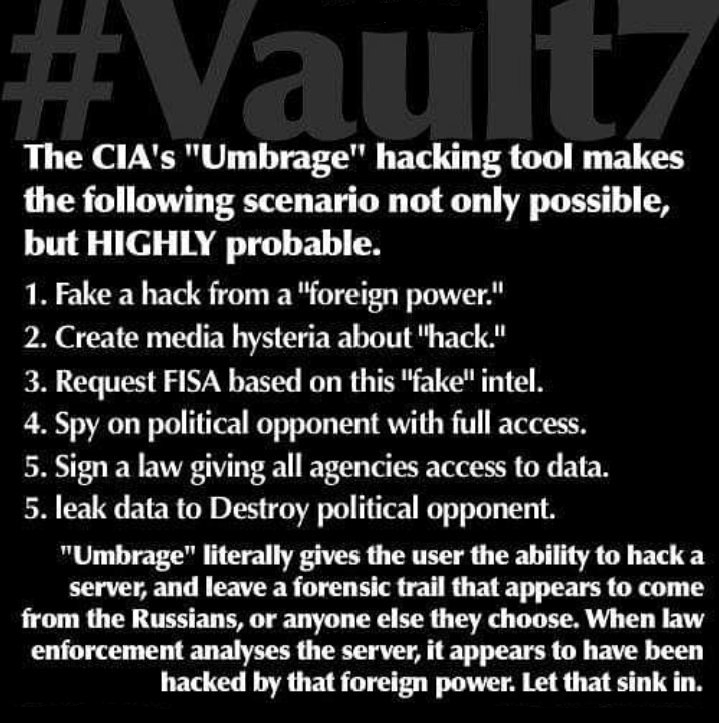
According to her, the group, known as UMBRAGE, is adept at hiding its online footprints. The existence of the team first came to light in a series of documents published by WikiLeaks in 2017 and subsequently picked up by American media. At the time, USA Today said that the shadowy operatives “may have been cataloguing hacking methods from outside hackers, including in Russia, that would have allowed the agency to mask their identity by employing the method during espionage.”


You must be logged in to post a comment.