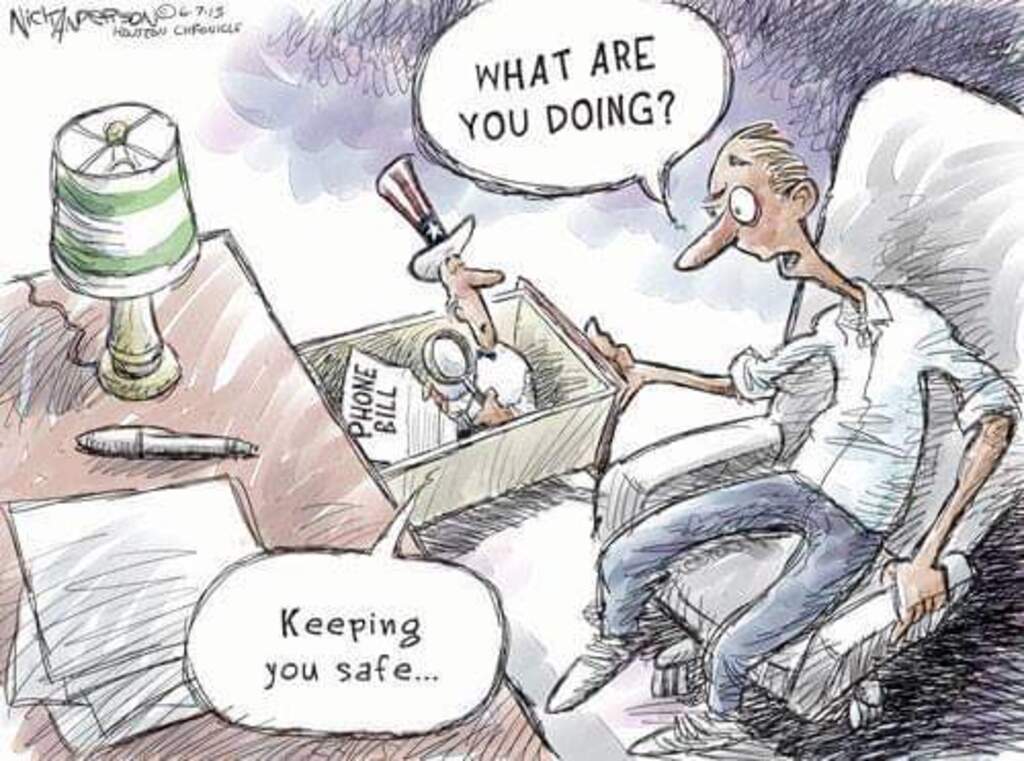
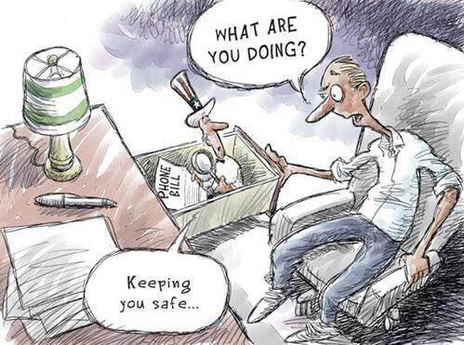
Most of the major US federal government websites and numerous state and local government websites are sending real-time surveillance data back to Google as users browse their websites. Even websites where users are submitting sensitive or personal information, such as the Federal Bureau of Investigation’s (FBI’s) tips page and the Internal Revenue Service (IRS) website, contain tracking code that sends real-time visitor data back to Google.
Most of these government websites contain tracking code from the web traffic analytics tool Google Analytics. This code collects detailed user data which is sent to Google’s servers, analyzed, and presented to website owners via an online dashboard.
Google Analytics automatically collects data on the pages visited, the time and duration of each visit, and other visitor data (such as the device, browser, operating system, and screen resolution of visitors). It can also be configured to collect data on more specific actions such as when users click or tap specific links, download content, or fill out forms.
Some government websites also have code from other Google services (such as DoubleClick, Google Adsense, Google Maps, Google Play, and YouTube) and other tech giants (such as Facebook, Microsoft, and Twitter) embedded on some of their pages.
The US government openly admits to using Google Analytics tracking code on 400 executive branch domains and 5,700 total websites. It even displays this surveillance data publicly via a real-time online dashboard which also tracks visitors with Google Analytics.


You must be logged in to post a comment.