
Albert Einstein on technology…


Cell phones are convenient devices, handily connecting us with loved ones, paying bills, accessing information—and treacherously reporting on our every move. Worse, even after the Supreme Court weighed in, many government agencies still insist that they have the right to pull up that tracking data to see our whereabouts. It’s increasingly apparent that, if you have your phone in your pocket, you may as well have a GPS beacon strapped to your ankle. If you want anonymity from the government, leave the gadget at home.
That point was illustrated in the wake of the Capitol riot, when the authorities pulled cell phone records to see who was present.
“In the hours and days after the Capitol riot, the FBI relied in some cases on emergency orders that do not require court authorization in order to quickly secure actual communications from people who were identified at the crime scene,” The Intercept reported this week. “Investigators have also relied on data ‘dumps’ from cellphone towers in the area to provide a map of who was there, allowing them to trace call records — but not content — from the phones.”
The data collected by people’s phones and the apps they use, often compiled by marketing firms, is amazingly detailed. An individual “outraged by the events of Jan. 6” supplied data on participants in the day’s events to The New York Times, whose writers were thoroughly creeped out by the information.
“While there were no names or phone numbers in the data, we were once again able to connect dozens of devices to their owners, tying anonymous locations back to names, home addresses, social networks and phone numbers of people in attendance,” Charlie Warzel and Stuart A. Thompson wrote.
Marketing databases have become a favorite resource for government agencies, which purchase the information as an attempted end-run around Fourth Amendment protections. The theory has been that, since the data is “voluntarily” provided to a third party there’s no privacy from the government required.
A damning new WSJ report says a small U.S. government contractor embedded software in over 500 apps, tracking millions of people worldwide.
A small U.S. company with ties to the U.S. defense and intelligence communities has embedded its software in numerous mobile apps, allowing it to track the movements of hundreds of millions of mobile phones world-wide, according to interviews and documents reviewed by The Wall Street Journal.
Anomaly Six LLC is the company in question, apparently boasting in marketing material that it was “able to draw location data from more than 500 mobile applications” from its own software development kit, embedded directly in some apps:
Anomaly Six says it embeds its own SDK in some apps, and in other cases gets location data from other partners.
The report says Anomaly Six is a federal contractor that provides global location data “to branches of the U.S. government and private-sector clients”. It told WSJ that it restricts the sale of U.S. mobile phone movement data only to the private sector, however.
If you’re using an Android device—or in some cases an iPhone—the Telegram messenger app makes it easy for hackers to find your precise location when you enable a feature that allows users who are geographically close to you to connect. The researcher who discovered the disclosure vulnerability and privately reported it to Telegram developers said they have no plans to fix it.
The problem stems from a feature called People Nearby. By default, it’s turned off. When users enable it, their geographic distance is shown to other people who have it turned on and are in (or are spoofing) the same geographic region. When People Nearby is used as designed, it’s a useful feature with few if any privacy concerns. After all, a notification that someone is 1 kilometer or 600 meters away still leaves stalkers guessing where, precisely, you are.
Independent researcher Ahmed Hassan, however, has shown how the feature can be abused to divulge exactly where you are. Using readily available software and a rooted Android device, he’s able to spoof the location his device reports to Telegram servers. By using just three different locations and measuring the corresponding distance reported by People Nearby, he is able to pinpoint a user’s precise location.
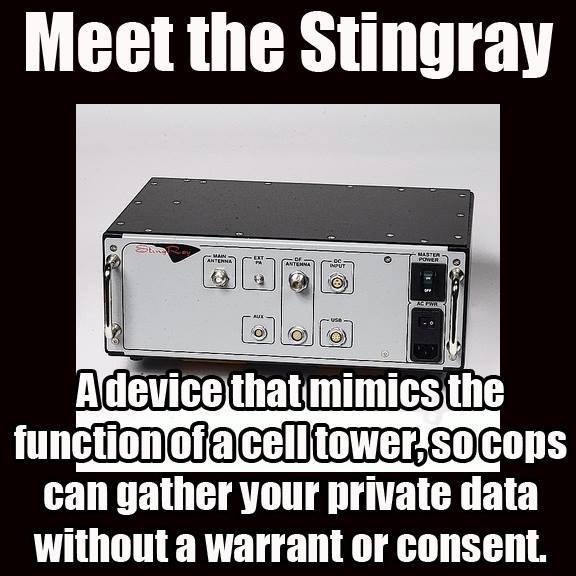
Digital rights advocates reacted with alarm to a report published Friday detailing how Defense Intelligence Agency analysts in recent years bought databases of U.S. smartphone location data without first obtaining warrants.
The Defense Intelligence Agency (DIA) is part of the Department of Defense and is tasked with informing military and civilian policymakers about the activities and intentions of foreign governments and nonstate actors.
The new revelation, first reported by the New York Times, initially came in the form of DIA responses to questions from Sen. Ron Wyden (D-Ore.) regarding the agency’s warrantless purchase of commercial location data generated by phones both inside and outside of the United States.
Wyden asked the DIA to clarify its interpretation of Carpenter v. United States, a 2018 U.S. Supreme Court decision barring law enforcement agencies from requesting personal location information from a cellphone company without first obtaining a search warrant from a judge.
“DIA does not construe the Carpenter decision to require a judicial warrant endorsing purchase or use of commercially-available data for intelligence purposes,” the agency replied, implicitly acknowledging its exploitation of an apparent loophole in the case that DIA believes permits its warrantless acquisition of location data from third-party brokers.
Aside from networking, companies use ultrasonic signals (or beacons) to gather information about users. That could include monitoring television viewing and web browsing habits, tracking users across multiple devices, or determining a shopper’s precise location within a store.
They use this information to send alerts that are relevant to your surroundings – such as a welcome message when you enter a museum or letting you know about a sale when you pass by a particular store.
But since this technology records sound – even if temporarily – it could constitute a breach of privacy. An analysis of various Australian regulations covering listening devices and surveillance reveals a legal grey area in relation to ultrasonic beacons.
A new lawsuit against Google filed on Thursday of last week raises interesting questions about whether or not the tech giant is “stealing Android users’ cellular data allowances though unapproved, undisclosed transmissions to the web giant’s servers”.
The suit, filed in US federal district court in San Jose by 4 plaintiffs aims to be certified as a class action. It alleges that Google is using Android users’ limited cellular data allowances to transmit information about the users unrelated to the use of Google services. The case surrounds “data sent to Google’s servers that isn’t the result of deliberate interaction with a mobile device”, according to The Register.
In other words, data transfers happening in the background, when the phone isn’t in use. The suit alleges that none of the four agreements accepted to participate in the Google ecosystem say anything about cell data transfers taking place in the background.
The suit states: “Google designed and implemented its Android operating system and apps to extract and transmit large volumes of information between Plaintiffs’ cellular devices and Google using Plaintiffs’ cellular data allowances.”
It continues: “Google’s misappropriation of Plaintiffs’ cellular data allowances through passive transfers occurs in the background, does not result from Plaintiffs’ direct engagement with Google’s apps and properties on their devices, and happens without Plaintiffs’ consent.”
The U.S. military is buying the granular movement data of people around the world, harvested from innocuous-seeming apps, Motherboard has learned. The most popular app among a group Motherboard analyzed connected to this sort of data sale is a Muslim prayer and Quran app that has more than 98 million downloads worldwide. Others include a Muslim dating app, a popular Craigslist app, an app for following storms, and a “level” app that can be used to help, for example, install shelves in a bedroom.
Through public records, interviews with developers, and technical analysis, Motherboard uncovered two separate, parallel data streams that the U.S. military uses, or has used, to obtain location data. One relies on a company called Babel Street, which creates a product called Locate X. U.S. Special Operations Command (USSOCOM), a branch of the military tasked with counterterrorism, counterinsurgency, and special reconnaissance, bought access to Locate X to assist on overseas special forces operations. The other stream is through a company called X-Mode, which obtains location data directly from apps, then sells that data to contractors, and by extension, the military.
You must be logged in to post a comment.